The recent paper from Google Quantum AI, published late Monday, has sparked considerable discussion online, particularly regarding its implications for Bitcoin. The report highlights a nine-minute attack scenario with a 41% chance of theft and potentially exposes around 6.9 million BTC.
However, the section addressing Ethereum did not receive as much attention but warrants further exploration.
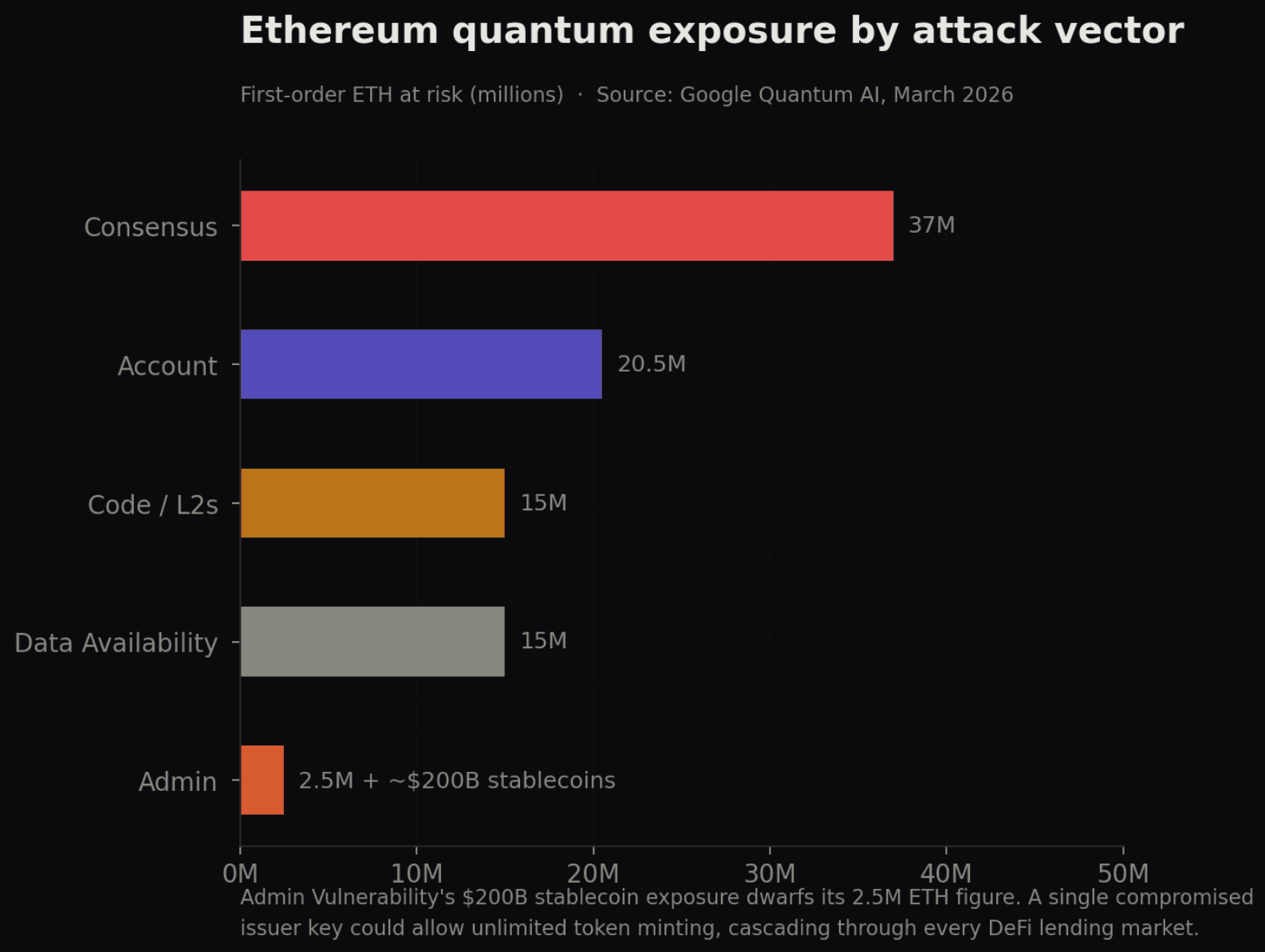
This whitepaper was co-authored by Justin Drake from the Ethereum Foundation and Dan Boneh from Stanford University. It outlines five distinct methods through which a quantum computer could target Ethereum, each focusing on different aspects of the network.
The total potential exposure exceeds $100 billion at current market valuations, with possible cascading effects that could be even more significant.
Wallets That Cannot Conceal
In Bitcoin transactions, users can keep their public keys—cryptographic identifiers linked to their funds—hidden behind hashes until they make a transaction. In contrast, once an Ethereum user initiates any transaction, their public key becomes permanently visible on the blockchain.
There is no method to change this key without completely abandoning the account. Google estimates that approximately 1,000 of the largest Ethereum wallets hold about 20.5 million $ETH, all vulnerable to exposure.
A quantum computer capable of cracking one key every nine minutes could potentially compromise all these wallets in less than nine days.
The Keys to Decentralized Finance (DeFi)
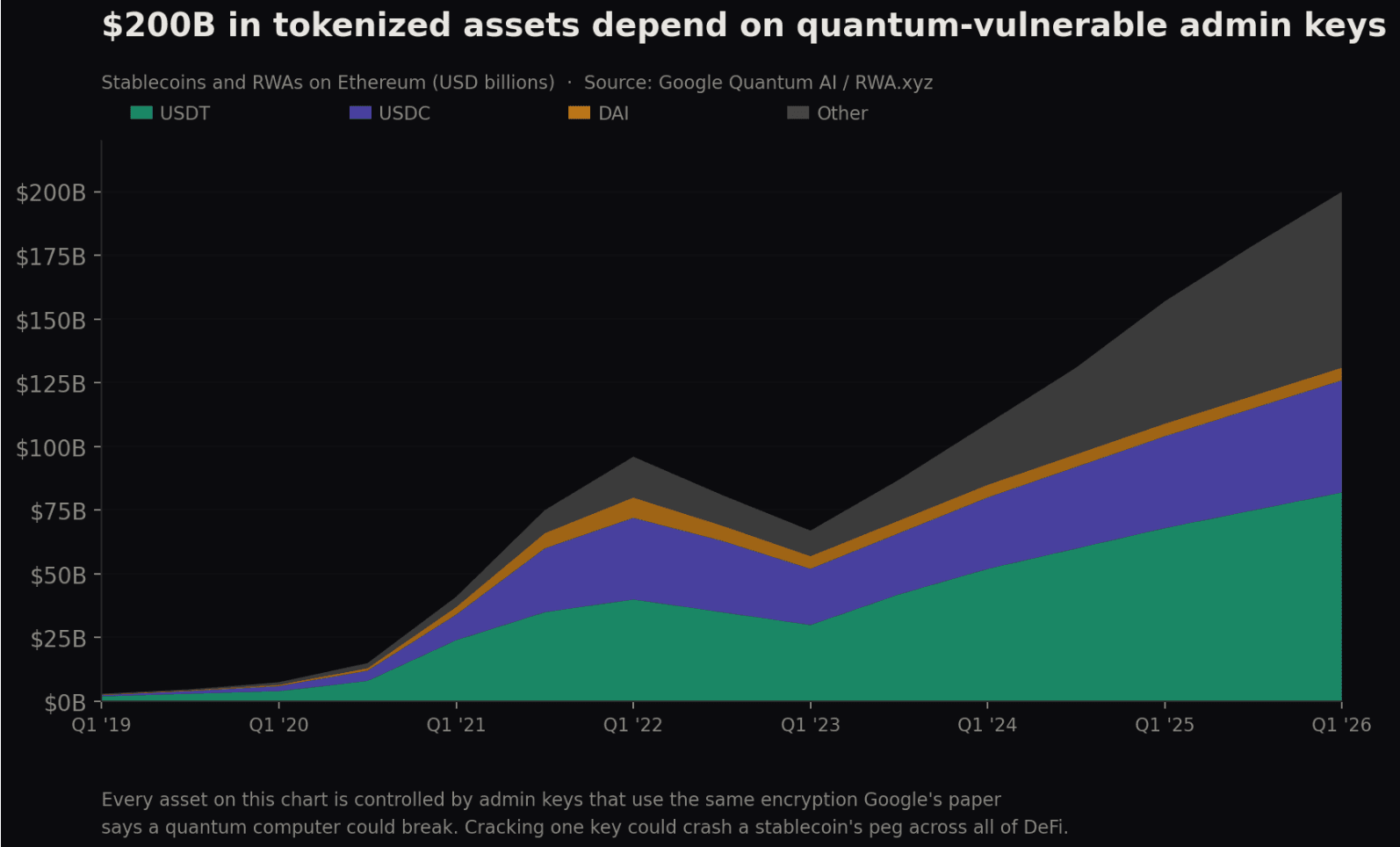
A multitude of smart contracts within Ethereum—self-executing programs responsible for lending activities and stablecoin issuance—grant specific privileges to select administrator accounts. These administrators possess powers such as pausing contracts or upgrading code and moving funds at will.
Google identified at least 70 significant contracts with exposed admin keys on-chain that collectively hold around 2.5 million $ETH. However, what’s more concerning is what these keys control beyond just $ETH.
Admin accounts also oversee minting rights for stablecoins like USDT and USDC; thus an attacker who successfully cracks one key could generate unlimited tokens without restriction. The research suggests that nearly $200 billion in stablecoins and tokenized assets on Ethereum rely heavily on these compromised admin keys.
If even one token were forged successfully it might trigger widespread disruption across all lending markets accepting those tokens as collateral.
Layer Twos Built On Fragile Mathematics
A substantial portion of transactions within Ethereum are processed via Layer Two networks such as Arbitrum and Optimism; these systems operate independently off the main chain before reporting back results.
This reliance means they depend upon cryptographic tools inherent in Ethereum’s architecture—all currently susceptible to quantum attacks.
The paper estimates over 15 million $ETH, spread across major L2s and cross-chain bridges may be vulnerable now due its lackluster security against quantum threats.
Only StarkNet employs alternative mathematics based upon hash functions rather than elliptic curves which offers protection against such vulnerabilities.
Pursuing Vulnerabilities Within Staking Systems
Ethereum utilizes proof-of-stake mechanisms where validators (participants locking up $ ETH ) vote validating transactions while authenticating those votes using digital signature schemes deemed weak against quantum computing capabilities.
Currently approximately thirty-seven million$ ETH is staked ; if attackers manage compromising one-third validator nodes , finalizing new blocks becomes impossible whereas controlling two-thirds allows them rewriting entire history chains .
The document indicates concentration staking large pools e.g., Lido holding roughly twenty percent increases risks targeting single provider infrastructure significantly shortening timelines needed launch successful assaults .
An Exploit Requiring Just One Execution
This particular vector lacks precedent within existing frameworks .Ethereum employs Data Availability Sampling verifying transaction data posted by Layer Two networks exists relying setup ceremony generating secret number intended destruction post-ceremony completion .
A capable Quantum Computer recovers secrets from publicly accessible datasets turning into permanent tool producing falsified verification proofs indefinitely needing access again after initial breach recovery occurs.
Google characterizes this exploit “potentially tradable.” Each dependent layer two utilizing blob data systems would face repercussions resulting fallout stemming breaches associated attacks launched therein.
Ethereums Head Start & Its Constraints
(Drake) co-author sits inside foundation launching post-quantum research portal last week backed eight years work testing networks shipping weekly multi-fork upgrade roadmap targets implementing resistant cryptography before year twenty-nine.
Ethereums twelve-second block times complicate real-time theft attempts compared ten-minute intervals seen bitcoin however papers clearly state enhancing base layers alone does not rectify thousands deployed smart contract codes protocols bridges requiring independent upgrades rotations occurring simultaneously controlled entities lacking centralized authority overseeing processes involved therein.